This senator is read into classified surveillance programs. When he says “look here,” we should look.
“So when Wyden asked whether the NSA was collecting data on millions of Americans, he was asking whether the wall between foreign and domestic surveillance, one of the foundational lines in how the American security state is allowed to operate, had quietly been taken down.
“Clapper said, “No, sir.”
Three months later, Edward Snowden’s leaks revealed that the NSA was, in fact, collecting phone metadata on essentially every call placed in the United States. Clapper had lied to Congress under oath
In March 2013, something interesting happened that almost nobody noticed at the time, but became enormous news three months later.
Senator Ron Wyden was questioning James Clapper, the Director of National Intelligence, in an open hearing of the Senate Intelligence Committee. Wyden asked him a simple question: “Does the NSA collect any type of data at all on millions or hundreds of millions of Americans?”
To understand why this question mattered, you have to understand what the NSA is supposed to be. The National Security Agency is a foreign intelligence agency. Its job is to spy on foreign governments, foreign militaries, and foreign nationals abroad. This kind of work would be flatly unconstitutional if pointed inward. Domestic investigations are supposed to belong to the FBI, which has to play by Fourth Amendment rules and requires warrants, probable cause, and judicial oversight.
The wall between the NSA and FBI exists for a reason: we have built all kinds of powerful tools for foreign surveillance, like bulk collection, warrantless interception, and dragnet monitoring. But the Constitution was written to expressly prohibit the government from turning this machinery of war and broad surveillance powers against its own citizens.
So when Wyden asked whether the NSA was collecting data on millions of Americans, he was asking whether the wall between foreign and domestic surveillance, one of the foundational lines in how the American security state is allowed to operate, had quietly been taken down.
Clapper said, “No, sir.”
Wyden pressed. Clapper added: “Not wittingly.”
Three months later, Edward Snowden’s leaks revealed that the NSA was, in fact, collecting phone metadata on essentially every call placed in the United States. Clapper had lied to Congress under oath. He later apologized for what he called his “clearly erroneous” testimony, claiming he’d given the “least untruthful” answer he could think of. He was never charged; the statute of limitations expired in 2018.
But let’s focus on the most relevant part of this story: Why did Wyden ask the question in the first place?
Wyden already knew the answer
Wyden sits on the Senate Intelligence Committee. It’s one of two committees (the other is in the House) whose members get read in to classified intelligence programs. It’s their job to make sure the intelligence community is operating above board. These committees are small, and the rest of Congress and the public stay in the dark, on a need-to-know basis.
So when Wyden asked Clapper whether the NSA was collecting data on millions of Americans, Wyden already knew the answer was yes. He’d been briefed. And when Clapper said “no,” Wyden knew, in real time, that the Director of National Intelligence was lying to Congress.
But Wyden couldn’t just stand up and tell the country what he knew. He was bound by classification rules. Asking the question in open session, with the answer pre-submitted to Clapper’s office a day in advance, was one of the only tools he had to let Congress know that he believed the intelligence community was running an illegal program.
He turned out to be right. In 2015, the Second Circuit ruled in ACLU v. Clapper that the NSA’s bulk phone records program exceeded what Congress had authorized under the Patriot Act. In 2020, the Ninth Circuit went further, holding that the program had violated federal surveillance law and was likely unconstitutional as well.
In fact, the 2015 court was pointed about why this mattered.
Congress, the judges wrote, “cannot reasonably be said to have ratified a program of which many members of Congress — and all members of the public — were not aware.”
Only a small circle of lawmakers on the intelligence committees knew. The rest of Congress, voting to reauthorize the Patriot Act, did not. Neither did the public. You cannot meaningfully consent to a program whose existence has been deliberately hidden from you.
But back to Wyden’s question: It’s a pattern worth remembering.
When Senator Wyden goes out of his way to ask a pointed question about a surveillance program, it’s usually because he already knows something he can’t say out loud.
Wyden: “Pay Attention To VPNs”
Which brings us to last week.
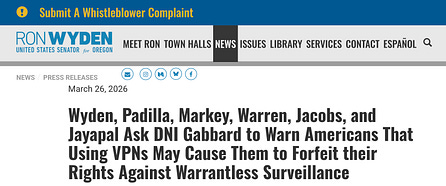
On March 26, 2026, Wyden (along with a handful of other Senators) sent a letter to the current Director of National Intelligence, Tulsi Gabbard. The letter asks Gabbard to publicly warn Americans that using a VPN may cause them to forfeit their Fourth Amendment rights against warrantless surveillance.
The mechanism is explained in Wyden’s press release: Under Section 702 of FISA and Executive Order 12333, when the U.S. government can’t tell what country a person is in, it’s allowed to assume that person is a foreigner. Foreigners outside the United States have no Fourth Amendment rights, and a VPN hides where you are.
So while these tools are used as a privacy protection, the intelligence community might be quietly stripping you of constitutional protections against your own government.
We don’t know exactly what Wyden has been briefed on. But the pattern from 2013 is clear: when he asks a pointed question in public, it’s usually because of something he can’t say out loud.
And then there’s the third-party doctrine
This Section 702 loophole is bad enough on its own. But there’s a second legal mechanism worth raising.
Under the third-party doctrine, U.S. law enforcement currently takes the position that it doesn’t need a warrant to obtain information you’ve voluntarily handed to a third party, such as your bank, your phone company, and your ISP. The doctrine traces back to the Katz “reasonable expectation of privacy” test: the Fourth Amendment kicks in only where you have a reasonable expectation of privacy, and the government’s argument is that once you’ve given data to someone else, that expectation disappears.
Now apply that to a VPN. A VPN routes 100% of your internet traffic through a third party. Under the government’s theory, that traffic is fair game without a warrant.
Which produces a genuinely absurd result: the legal system says you have no reasonable expectation of privacy in data you handed to a service whose entire purpose is privacy. The tool you bought specifically to assert a privacy interest is recharacterized as the act of waiving it.
In Carpenter v. United States (2018), the Supreme Court carved an exception into the third-party doctrine, holding that the government does need a warrant to obtain historical cell-site location data, on the theory that some kinds of third-party data are too revealing to fall under the old rule. VPN traffic seems like an even stronger candidate. It might be time for someone who uses a VPN to sue the government.
Ludlow Institute’s NBTV Newsletter is funded by community support. Consider becoming a free or paid subscriber.
What Now?
So should we, or should we not, be using a VPN? The honest answer is that there’s no clean solution, because the problem isn’t really VPNs. The problem is that the entire modern internet is built on handing your data to third parties, such as your ISP, your DNS resolver, your email provider, the ad networks embedded in every website you visit, and so on. And the third-party doctrine turns every one of those interactions into a warrantless surveillance opportunity. A VPN just shifts which third party holds your traffic, it doesn’t change the underlying legal theory that says the government can help itself to it without a warrant.
That said, I still use a VPN, and I’m going to keep using one. I don’t want my IP address handed to every website I interact with, and the protection a VPN offers against that is real, even if it’s narrower than the marketing suggests. But it’s really important to be careful about which one. As I covered in a previous video, an overwhelming number of VPN providers are just data-collection shells, and some are outright malware. “Use a VPN” isn’t the advice. “Use a VPN you’ve actually vetted” is closer.
Longer term, it’s time to explore the tools that can’t aggregate your data in the first place. I’ve been digging into decentralized VPNs and mixnets lately, and if you’ve used any, I’d love to hear about your experience.
But the deeper fix is actually legal: The third-party doctrine is a relic of a world where “data you gave to someone else” meant a very narrow scope of information. It does not belong in a digital age that turns everything we do into data held by someone else.
As long as the third-party doctrine stands, we lose one of the most important protections we have against the government’s ability to surveil its own citizens: the warrant requirement. It’s a loophole the size of the entire internet. Closing that loophole is how we get the Fourth Amendment back.
Yours In Privacy,
Naomi
Consider supporting our nonprofit so that we can fund more research into the surveillance baked into our everyday tech. We want to educate as many people as possible about what’s going on, and help write a better future. Visit LudlowInstitute.org/donate to set up a monthly, tax-deductible donation.

