https://consortiumnews.com/2020/10/26/the-revelations-of-wikileaks-no-9-opening-the-cias-vault/
By Patrick LawrenceSpecial to Consortium News
On Feb. 6, 2017, WikiLeaks released documents detailing the Central Intelligence Agency’s espionage program in the months leading up to and following France’s presidential election in 2012.
The agency used spies and cyberweapons to infiltrate and hack into the major political parties with competing candidates — the Socialists, the National Front and the Union for a Popular Movement. Their candidates — respectively François Hollande, Marine Le Pen and incumbent Nicolas Sarkozy — were also spied upon individually, as were many other prominent political figures.
The objectives of the program included ascertaining the contending parties’ political strategies and platforms, their views of the U.S., and their relations with the European Union, with other European nations (Germany, Britain) as well as Israel, Palestine, Libya, Syria, and others. The CIA’s French operation lasted 10 months, beginning in November 2011 and enduring until September 2012, several months after Hollande won the election and formed a Socialist government.
WikiLeaks’ disclosure of the agency’s project bears a special irony: It was just as WikiLeaks published this material in 2017 that the CIA helped propagate unsubstantiated (and later discounted) “intelligence” that Russian hackers and propagandists were interfering with France’s presidential election that year. Similar allegations (similarly lacking in evidence) were floated as the European Union held parliamentary elections in May 2019.
As WikiLeaks reported at the time of the releases on the CIA’s covert activities in France, those revelations were to serve “as context for its forthcoming CIA Vault 7 series.” WikiLeaks’ apparent intent was to display a CIA’s hacking operation in action.
Vault 7, the subject of this latest report on the history of WikiLeaks disclosures, stands as the most extensive publication on record of classified and confidential CIA documents. Never before and not since have the agency’s innumerable programs and capabilities been so thoroughly exposed to public scrutiny.
Biggest Since Snowden
Rally in Germany in support of Edward Snowden, Aug. 30, 2014. (Markus Winkler, CC BY-SA 2.0, Wikimedia Commons)
Julian Assange, WikiLeaks founder and publisher, described the Vault 7 publications as the most significant since Edward Snowden, the former CIA data analyst, released an unprecedented trove of National Security Agency documents in the summer of 2013.
The Vault 7 series concerns the extraordinarily sophisticated inventory of cyber weapons the CIA has developed to spy on or hack into the communications of any person or entity it targets. Apart from the espionage function, certain of the programs in Vault 7 — this designation is WikiLeaks’, not the CIA’s — can also plant documents and data without being detected as the source — when, for example, the agency wishes to compromise an adversary via a false-flag operation.
The program wherein this capability was developed, called Marble, may have been crucial to creating the orthodox “narrative” that Russia was responsible for the theft of Democratic Party email in 2016 — the cornerstone allegation in the construct we now call Russiagate.
The Vault 7 releases expose the CIA’s hacking activities from 2013 to 2016. The series began on March 7, 2017, with the publication of “Year Zero,” an introductory survey and analysis of the agency’s globally deployed hacking programs. The Vault 7 series ran for six months, concluding on Sept. 7, 2017.
Complete as of that date, the series is comprised of 23 publications, each of which focuses on an individual hacking or cyber-espionage program. Marble is one of these.
The CIA’s development of its hacking capabilities began as a joint effort with the National Security Agency. But the Sept. 11 terrorist attacks and the subsequent wars in Afghanistan and Iraq, begun in 2001 and 2003 respectively, proved a turning point for the agency. It was during this time that the CIA, as WikiLeaks puts it in its introduction to the Vault 7 series, “gained political and budgetary preeminence over the NSA.”
According to former U.S. intelligence sources, the CIA has invested some $175 billion in its vast variety of cyber programs in the post–2001 years. “The agency’s hacking division, WikiLeaks notes, “freed it from having to disclose its often controversial operations to the NSA (its primary bureaucratic rival) in order to draw on the NSA’s hacking capacities.”
A Near Deal to Free Assange
Assange in 2014, while in the Ecuadorian embassy in London. (Cancillería del Ecuador, CC BY-SA 2.0, via Wikimedia Commons)
WikiLeaks launched the Vault 7 series at a delicate moment for Assange, who was at the time taking asylum at the Ecuadoran embassy in London.
Shortly after Donald Trump took office in January 2017, Assange’s attorneys approached a lawyer named Adam Waldman, who was noted for his Washington connections.
Assange’s team proposed negotiations that would commit the U.S. to granting Assange limited immunity and safe passage from the Ecuadoran embassy in exchange for his agreement to limit publication of classified CIA documents. The agency knew by this time that WikiLeaks had an extensive inventory of CIA documents it was prepared to publish. These included what WikiLeaks soon named Vault 7.
Crucially, Assange signaled that he was also willing to reveal technical evidence that would shed light on who was not responsible for the theft of email from the Democratic National Committee in mid–2016. This was key: By this time the “narrative” that Russia had hacked the DNC’s computer servers was well-established; the Democratic Party, the intelligence agencies, the Federal Bureau of Investigation and the media were heavily invested in it. Assange, while observing the WikiLeaks principle of not revealing sources, had by this time asserted that Russia had nothing to do with the intrusion.
The Justice Department and Assange’s attorneys drafted an immunity deal in the course of the negotiations that both sides agreed to pursue. The attorneys’ initial contact, through Waldman, was a DoJ official named Bruce Ohr. The lead DoJ negotiator was named David Laufman. When WikiLeaks released “Year Zero” on March 7, 2017, these negotiations were still in progress; the release had no apparent impact on the talks.
But at this point the contacts between Assange and the U.S. government took a fateful turn. The only full account of the events summarized below was written by John Solomon, who has followed the Russiagate phenomenon from the first, and was published in The Hill on June 25, 2018.
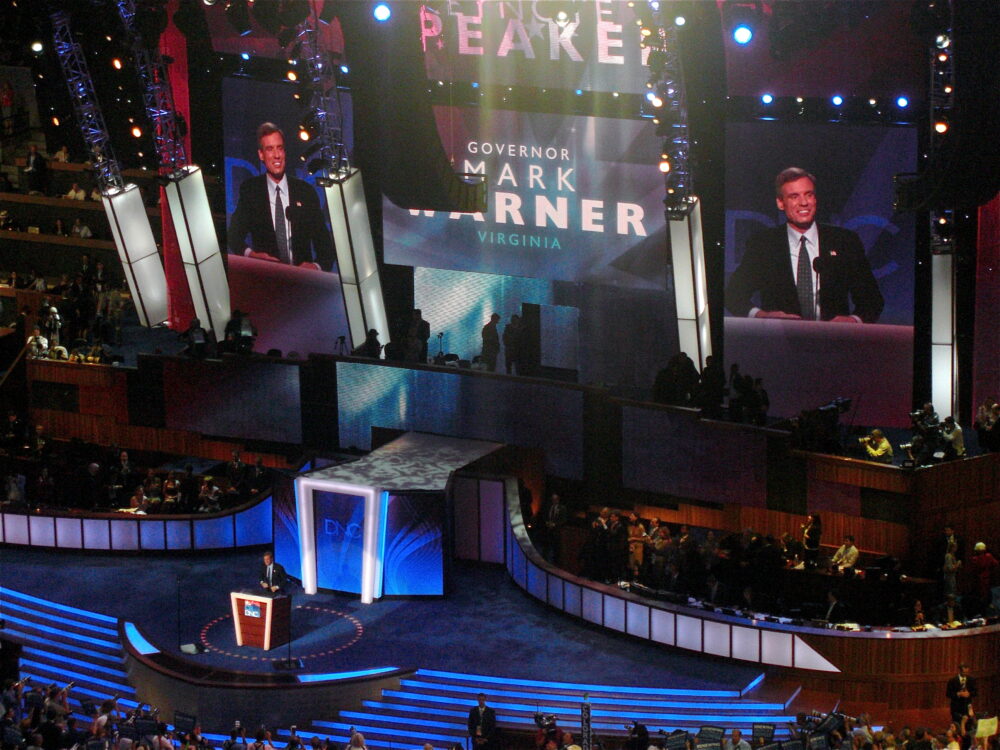
Shortly after negotiations began, Waldman, the go-between, contacted Mark Warner, the Democratic senator from Virginia, to see if the Senate Intelligence Committee, of which Warner was vice-chairman, wished to contact Assange on its own in connection to matters related to Russia. This proved a miscalculation.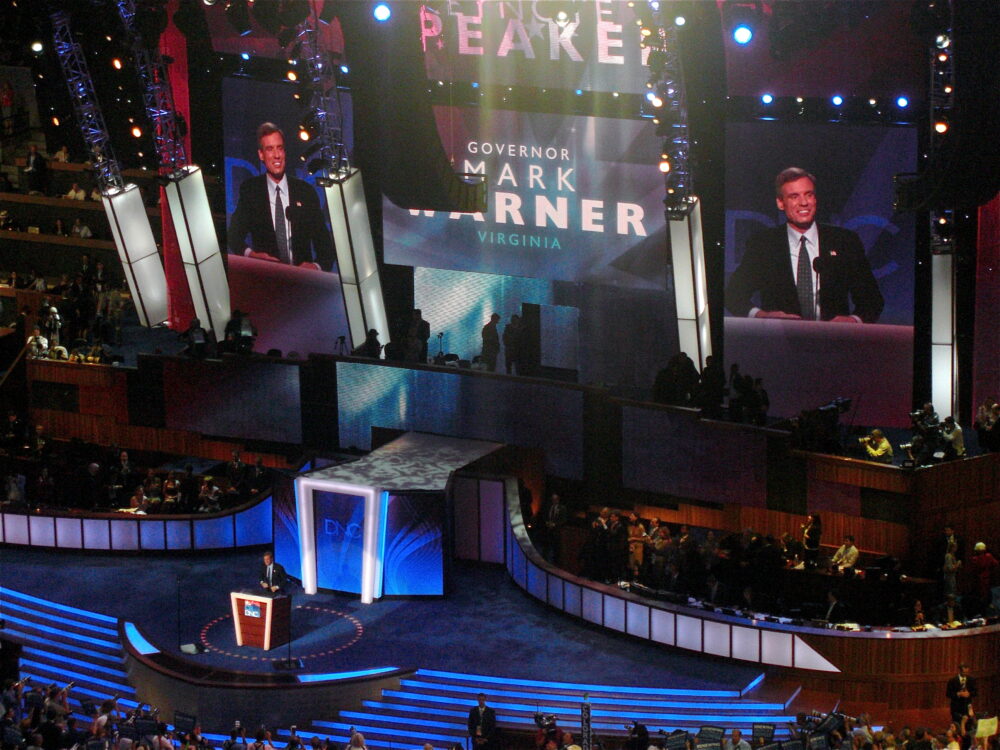
Sen. Mark Warner giving keynote address during 2008 Democratic National Convention in Denver. (Qqqqqq, CC BY-SA 3.0, Wikimedia Commons)
Warner, who had vigorously pressed the Russiagate narrative from the first, soon contacted James Comey, then the FBI director. Comey was also an aggressive Russiagate advocate and had a direct interest in sustaining the official account of events: It was while he ran the FBI that the bureau worked with CrowdStrike, the infamous cybersecurity firm hired by the DNC, to build what is now demonstrated to be an entirely false case to support the Democrats’ assertions of Russian responsibility for the mail intrusion.
Any proof that Russia had no role in the DNC mail theft would have discredited the FBI and Comey and very likely destroyed the career of Comey and numerous others.
Comey, working through Sen. Warner, immediately ordered Waldman to cut off the Assange–DoJ talks. Although negotiations continued a brief while longer, Comey had effectively dealt them a soon-to-be-fatal blow. By this time WikiLeaks had released two other Vault 7 document collections, including what it called the Marble Framework.
The DoJ finally broke off the negotiations on April 7, when WikiLeaks released a fourth set of documents, this one called Grasshopper. Six days later Mike Pompeo, then CIA director, gave a notably aggressive speech at the Center for Strategic and International Studies, the Washington think tank, in which he called WikiLeaks “a nonstate hostile intelligence service often abetted by state actors like Russia.” https://www.youtube.com/embed/pe3ApagvwNM?enablejsapi=1&autoplay=0&cc_load_policy=0&iv_load_policy=1&loop=0&modestbranding=1&fs=1&playsinline=0&controls=1&color=red&rel=0&autohide=2&theme=dark&
With the CSIS speech, Pompeo effectively opened the Trump administration’s rigorously pressed campaign to have Assange extradited from Britain. The WikiLeaks founder appears never to have had another chance to negotiate an agreement providing for his freedom.
Run Amok
The Vault 7 releases continued at a steady pace, roughly four a month, for the next five months. The documents WikiLeaks made public, along with descriptions of the programs WikiLeaks deemed significant, can be found via its “Vault 7: Projects” report. Taken together they describe an expensively funded U.S. government organization that has run frighteningly amok, operates with no regard for U.S. or international law, and stands entirely beyond civilian control. Many of the projects exposed in the Vault 7 releases, and very likely most or all, violate Fourth Amendment rights to privacy and the CIA’s charter, which bars the agency from activity on U.S. soil.
Former CIA Director Allen Dulles. (CIA)
The history of the CIA, reaching back to Allen Dulles’ tenure as director (1953 to 1961), indicates that from its earliest days it entertained a diabolic desire to accumulate the power to operate with no reference to constraints of any kind, including those imposed by ordinary standards of decency. In this way it was effectively the id of America’s exceptionalist consciousness. What we see in the Vault 7 series is the perversely logical outcome of this culture of limitless impunity and immunity.
By the end of 2016, the hacking division of the CIA’s Center for Cyber Intelligence had more than 1,000 hacking, malware, virus-implanting, remote-control and Trojan-horse programs in its inventory. These comprised more than 700 million lines of computer code.
Former CIA and NSA officials told Consortium News that a line of code costs roughly $25 to produce, putting the cost of the agency’s hacking tools over the years these programs were developed at $175 billion. “The CIA had created its ‘own NSA,’” WikiLeaks noted when it began releasing the Vault 7 publications, “with even less accountability and without publicly answering the question as to whether such a massive budgetary spend on duplicating the capacities of a rival agency could be justified.”
What follows are accounts and summaries of the most significant of the 23 Vault 7 releases. We present these chronologically, the earliest first, to give readers a clear idea of how WikiLeaks organized and presented the Vault 7 project.
Year Zero
March 7, 2017
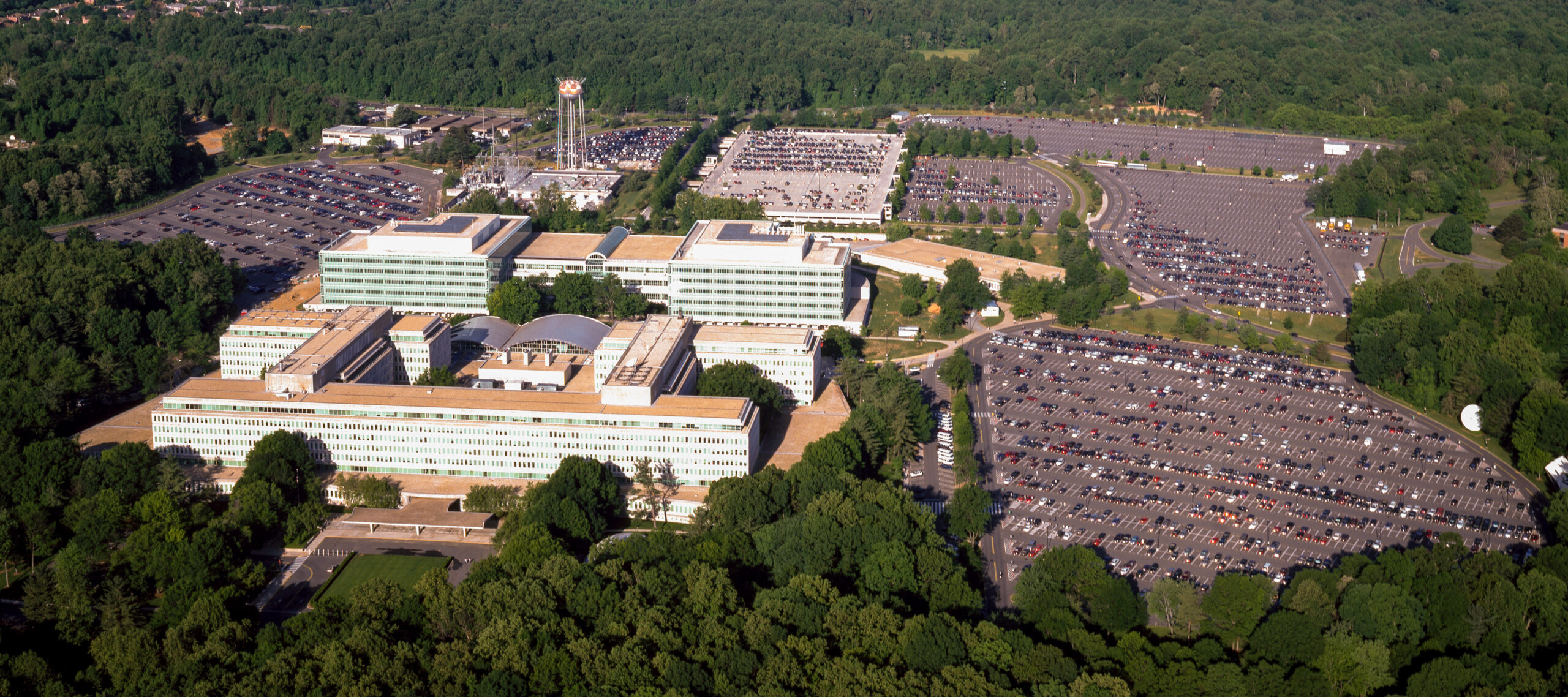
With the publication of “Year Zero,” it was immediately clear that WikiLeaks had penetrated into or very near the core of the CIA’s cyberoperations. This first Vault 7 release is comprised of 8,761 documents and files obtained from what WikiLeaks describes as “an isolated, high-security network situated inside the CIA’s Center for Cyber Intelligence in Langley, Virginia, the agency’s headquarters.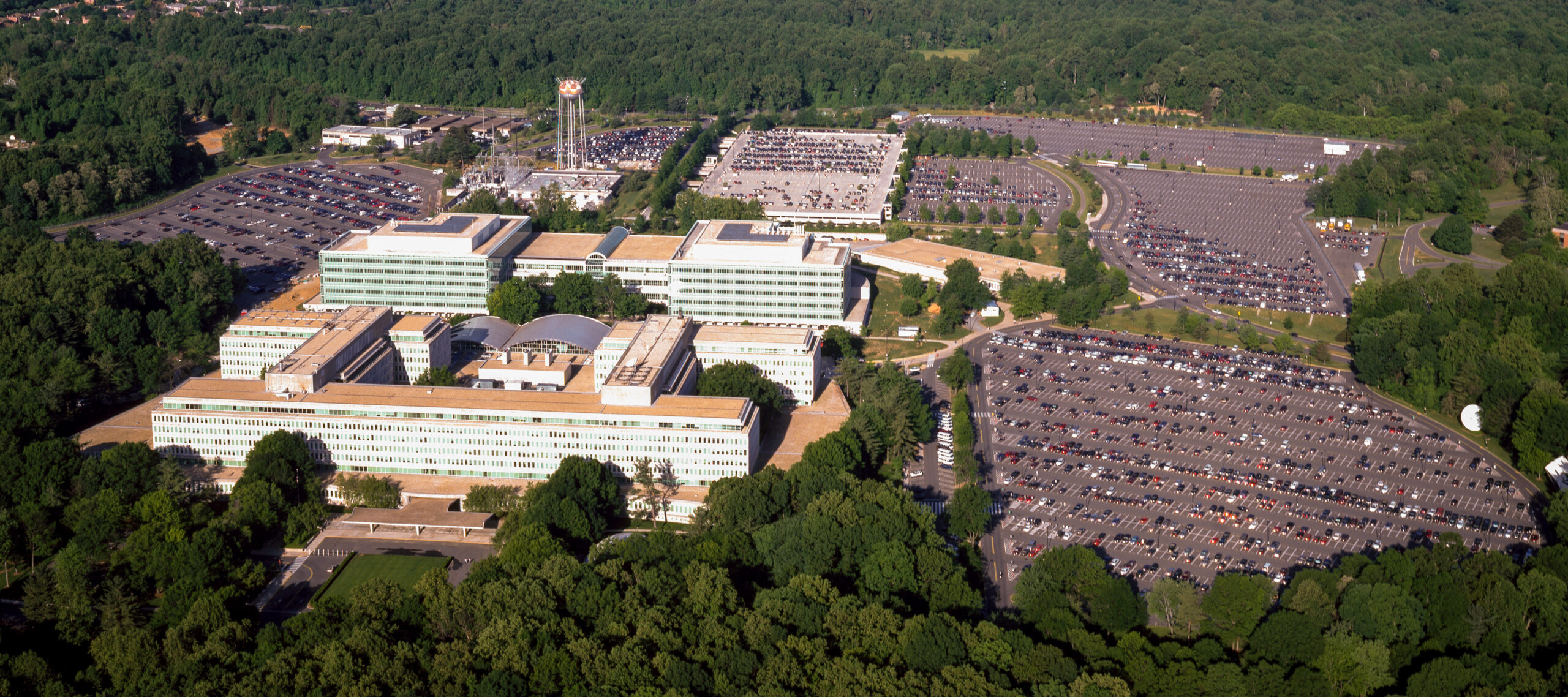
Aerial view of CIA headquarters in Langley, Virginia. (Carol M. Highsmith, Wikimedia Commons)
As WikiLeaks notes, the agency had “lost control of the majority of its hacking arsenal” shortly before it published “Year Zero.” There had been a massive leak, to put this point in simple terms. “The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner,” WikiLeaks reported, “one of whom has provided WikiLeaks with portions of the archive.” This occurred at some point in 2016.
“Year Zero” serves as an overview of “the scope and direction of the CIA’s global hacking program” and an introduction to material included in the Vault 7 releases to follow. The agency’s inventory of tools was the purview — and we can assume continues to be so — of the Engineering Development Group (EDG), a technology department under the authority of the Center for Cyber Intelligence.
The EDG also tests and operates its products once they are perfected and added to the agency’s arsenal. The engineering group, Wikileaks reported, has developed some 500 projects, each with its own malware and hacking tools. The EDG’s focus is on penetration, implanting, control and exfiltration. “Year Zero” analyzes the most important of these.
High among the objectives of Vault 7 programs was to achieve the capability of penetrating the manufacturers of cellular telephones and other electronic devices for a variety of operations. Among the products targeted for this purpose were Apple’s iPhone and iPad, Google’s Android operating system, Microsoft Windows and Samsung televisions.
Programs included in the Vault 7 collection were designed to hack these and other commonly used devices and systems remotely so they can corrupt the targets and also send the CIA the owner’s geographic location and all audio and text communications. Other programs were capable of turning on a device’s microphone and camera without the owner’s knowledge. Other attack-and-control programs targeted MAC OS X, Solaris and Linux operating systems.
A number of the CIA’s programs revealed in the Vault 7 releases focus exclusively on one or another of these companies, most commonly Microsoft.
Building 92 at Microsoft Corporation headquarters in Redmond, Washington. (Coolcaesar, CC BY-SA 4.0, Wikimedia Commons)
“Grasshopper” (April 7, 2017) is a platform for the development of malware designed for attacks on Windows operating systems. “AfterMidnight” (May 12, 2017) and “Brutal Kangaroo” (June 22, 2017) also target the Microsoft Windows platform, while “Weeping Angels” (April 21, 2017) infiltrated Samsung televisions. “Outlaw Country” (June 30, 2017) is designed for attack on computers that use the Linux OS.
“Year Zero” also details the CIA’s use of what the agency calls “zero days.” These are commonly occurring software code imperfections and vulnerabilities in electronic devices that the CIA knows and makes use of but does not disclose to manufacturers or the public.
In some respects, zero days are treated as commodities. While the CIA discovered some zero days on its own, it obtained others from the NSA, GCHQ (the NSA’s British counterpart), or the FBI. It also purchased zero days from private cyber-weapons manufacturers much as the Pentagon would buy a weapons system from a defense contractor.
The CIA’s stockpile of zero days enables it to bypass encryption systems installed in such communications applications as WhatsApp, the widely used long-distance telephone and text service. This makes zero days, which can be used either locally or remotely, especially significant in extending the reach of the agency’s hacking operations. The CIA’s practice of keeping zero days secret — effectively hoarding them, as WikiLeaks notes — is especially cynical and dangerous.
As WikiLeaks explains:
“If the CIA can hack these phones then so can everyone else who has obtained or discovered the vulnerability. As long as the CIA keeps these vulnerabilities concealed from Apple and Google (who make the phones) they will not be fixed, and the phones will remain hackable. The same vulnerabilities exist for the population at large, including the U.S. Cabinet, Congress, top CEOs, system administrators, security officers and engineers. By hiding these security flaws from manufacturers like Apple and Google, the CIA ensures that it can hack everyone– at the expense of leaving everyone hackable.”
Most malware developed by the EDG and related units in the CIA’s organizational structure is designed to remain in implanted devices for considerable lengths of time — in some cases years — after it is installed. So long as it is present it communicates regularly and in two-way fashion with the CIA’s Command and Control systems.
While many programs are implanted remotely, some require a physical presence. This typically means an agent infests a targeted device on site. But in some cases, the CIA covertly intervened into supply chains and delivery services, including postal services, by opening, infecting, and on-sending products without the knowledge of either the manufacturer or the purchaser.
As it began its Vault 7 series with “Year Zero,” WikiLeaks took the occasion to note “an extreme proliferation risk in the development of cyber ‘weapons,’” as Assange put it at the time. He drew a comparison between these weapons and the global arms trade, noting “the inability to contain them, combined with their high market value.”
The source of the Vault 7 trove, who was among the former government hackers and contractors circulating the Vault programs among themselves, shared these and other concerns:
“In a statement to WikiLeaks the source details policy questions that they say urgently need to be debated in public, including whether the CIA’s hacking capabilities exceed its mandated powers and the problem of oversight of the agency. The source wishes to initiate a public debate about the security, creation, use, proliferation, and democratic control of cyber-weapons.”
This is Consortium News’s intent in publishing its report on Vault 7.
Mindful of the risks attached to proliferation, and perhaps of past (and unfounded) charges that its publications compromised U.S. national security and American personnel, WikiLeaks notes that it was careful to avoid distributing what it termed “‘armed’ cyber-weapons” as it published the Vault 7 series.
It also said it redacted “tens of thousands of CIA targets and attack machines throughout Latin America, Europe, and the United States.” In a note in an FAQ section appended to “Year Zero,” WikiLeaks states, “Names, email addresses, and external IP addresses have been redacted in the released pages (70,875 redactions in total) until further analysis is complete.”
Dark Matter
March 23, 2017
Projects developed in the “Dark Matter” program were designed to penetrate Apple Macs and iPhones with what is called firmware — that is, malware that continues to infect the units attacked even if the OS is reinstalled. “Sonic Screwdriver,” a sub-project in this group, allowed attackers to install and activate computer code while users booted up these Apple devices.
See the rest here
Patrick Lawrence, a correspondent abroad for many years, chiefly for theInternational Herald Tribune, is a columnist, essayist, author and lecturer. His most recent book is Time No Longer: Americans After the American Century (Yale). Follow him on Twitter @thefloutist. His web site is Patrick Lawrence. Support his work via his Patreon site.
Be seeing you